Dominion Cyber Articles

Search...

Decentralized Identity Management Securing User Identity in a Fragmented Digital World
In a fragmented digital world where individuals interact with various online platforms and services, user identity management plays a crucial role in maintaining privacy, security, and trust. The challenges of traditional identity management approaches, such as centralized systems, have paved the way for decentralized identity solutions. Decentralized identity, also known as self-sovereign identity, is an emerging concept that aims to provide individuals with greater control and ownership over their digital identities. It operates on the principles of privacy, security, and user consent. Decentralized identity works by leveraging technologies like blockchain to enable secure and verifiable interactions between users, service providers, and other entities. It eliminates the need for centralized authorities and offers several advantages over traditional systems. The advantages of
The Rise of Fileless Malware Detection and Countermeasures
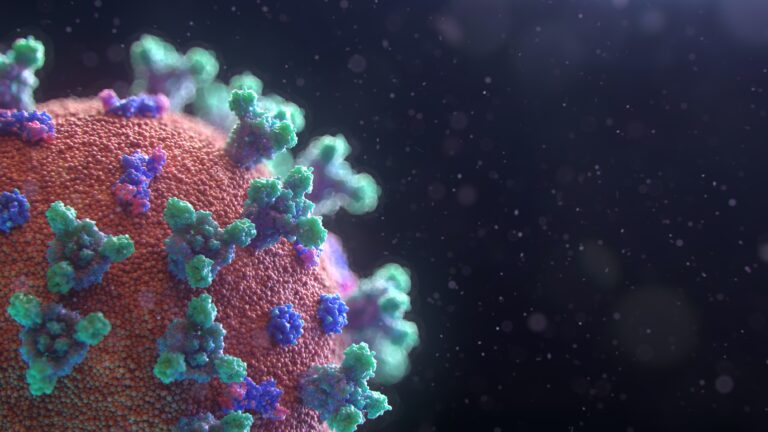
As technology continues to advance, so do the tactics used by cybercriminals. One such method that has gained prominence in recent years is fileless malware. This article explores the rise of fileless malware, its detection, and countermeasures to mitigate this growing threat. Fileless malware, as the name suggests, is a type of malicious software that operates without leaving traces of files or executables on the victim’s system. It is designed to exploit vulnerabilities in the operating system or legitimate applications, making it difficult to detect and remove. Unlike traditional malware, fileless malware resides in the computer’s memory, registry, or scripts, allowing it to evade traditional antivirus software. Understanding how fileless malware works is vital in combating this cyber threat. It

Penetration Testing IoT Devices Challenges and Approaches in the Connected World
Penetration testing is a vital process in ensuring the security and integrity of IoT (Internet of Things) devices in our connected world. It involves actively and methodically evaluating the security measures of these devices to identify vulnerabilities and weaknesses that could be exploited by malicious attackers. This article will explore the concept of penetration testing for IoT devices, its significance, the challenges faced, and the approaches that can be adopted to effectively test the security of these devices. Penetration testing is important for IoT devices due to several reasons. Firstly, it helps in protecting against malicious attacks, ensuring that these devices are secure and not susceptible to unauthorized access or data breaches. Secondly, penetration testing helps in identifying vulnerabilities and

Secure Software Development Life Cycle SDLC Integrating Security from Inception to Deployment
The Secure Software Development Life Cycle (SDLC) is an approach that emphasizes the integration of security measures and practices throughout the software development process. From the inception of a software project to its deployment and maintenance, security is given utmost importance to ensure the protection of sensitive data, prevention of security breaches, and mitigation of potential risks. By following the SDLC, organizations can systematically address security requirements and implement security controls at each stage of the software development process. This comprehensive approach improves the overall security posture of the software and reduces the likelihood of vulnerabilities and exploits. Integrating security in the SDLC is of paramount importance due to the increasing threats and risks associated with software development. By incorporating
The Role of Quantum Computing in Cybersecurity Threats and Opportunities
The emergence of quantum computing has the potential to revolutionize various industries, including cybersecurity. Quantum computing utilizes the principles of quantum mechanics to perform complex computations at an exponential speed, far surpassing the capabilities of traditional computers. In the realm of cybersecurity, quantum computing presents both threats and opportunities. The threats posed by quantum computing in cybersecurity are multifaceted. Firstly, current encryption methods, which rely on the difficulty of factoring large numbers, can be easily broken by quantum computers using Shor’s algorithm. This could render sensitive data vulnerable to unauthorized access. Weaknesses in the Public Key Infrastructure (PKI) used for secure communication and digital signatures could be exploited by quantum computers. The increased speed of quantum computing could accelerate cyber
Cybersecurity and Privacy Regulations A Comparative Analysis across Different Jurisdictions
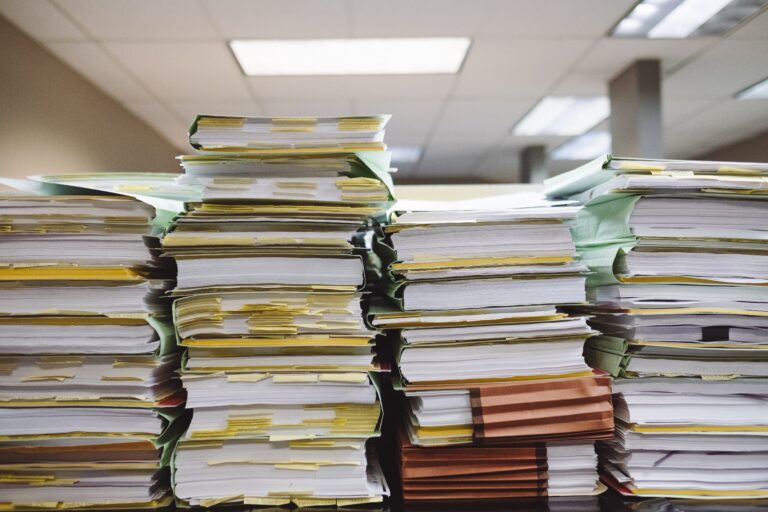
Cybersecurity and privacy regulations play a critical role in today’s digital landscape, ensuring the protection of personal data, safeguarding national security, and mitigating cyber threats. Understanding the regulatory frameworks across different jurisdictions is essential for individuals, organizations, and governments to effectively navigate the complex landscape of cybersecurity and privacy. The importance of cybersecurity and privacy regulations can be understood through the following key points: Protection of Personal Data: Regulations aim to protect individuals’ personal data, ensuring that it is handled securely, preventing unauthorized access, use, or disclosure. Safeguarding National Security: Cybersecurity regulations contribute to safeguarding national security by protecting critical infrastructure, preventing cyber attacks, and ensuring the availability, integrity, and confidentiality of sensitive information. Mitigating Cyber Threats: Regulations address emerging

SpiderFoot: An Open-Source OSINT Automation Tool for Cybersecurity
Introduction SpiderFoot is an open-source OSINT automation tool designed for cybersecurity purposes. It offers a wide range of functionalities that can be utilized by professionals to gather intelligence and perform investigations. The tool provides an efficient and automated solution to extract relevant information from various sources, including websites, social media platforms, and public databases. SpiderFoot is a valuable asset for cybersecurity professionals, as it enables them to streamline their research process and obtain crucial insights. Its capabilities make it an indispensable tool in the constantly evolving realm of cybersecurity. Moreover, SpiderFoot stands out from other tools due to its user-friendly interface and extensive customization options. It allows users to tailor their investigations according to specific requirements, maximizing efficiency and accuracy.

Persistence: How To Maintain System Access within Linux
Establishing Persistence in Linux: Techniques and Strategies In cyber security understanding how attackers exploit vulnerabilities to gain unauthorized access and maintain control over compromised systems is crucial. One prevalent tactic involves establishing persistence in Linux environments, where attackers set up mechanisms to regain access after system reboots. This article delves into various techniques attackers employ to achieve this, shedding light on the potential risks and countermeasures for defenders and system administrators. 1. Cron Jobs: Scheduled Intrusion Cron jobs, commonly used for automating tasks on Linux systems, can be exploited by attackers to execute malicious scripts periodically. By inserting malevolent tasks into the cron scheduler, attackers ensure that their code continues to run even after the system restarts, maintaining
Ultimate Guide to Installing Portainer CE on Docker for Linux Users
Portainer is an open-source tool that provides a management UI for Docker environments. With Portainer, users can manage containers, images, networks, volumes, and more, all from a web-based dashboard. It simplifies certain Docker tasks, making it easier for users who might not be familiar with the Docker CLI. Explanation: Remember, Portainer also offers advanced features such as user management, templates, application deployment, and more. It’s a powerful tool for both beginners and advanced Docker users.
Docker Unveiled: Your Comprehensive Guide to Understanding and Installing Docker
Docker Unveiled: Your Comprehensive Guide to Understanding and Installing Docker Introduction Docker is a platform that allows developers to create, deploy, and run applications in containers. A container is a lightweight, standalone, executable software package that encompasses everything needed to run a piece of software, including the code, runtime, system tools, libraries, and settings. Containers are isolated from each other and from the host system, which allows them to run consistently across different environments. Key features of Docker include: Docker uses a client-server architecture. The Docker client communicates with the Docker daemon, which does the heavy lifting of building, running, and managing containers. Docker images are built from Dockerfiles and stored in a registry (like Docker Hub) from which they
